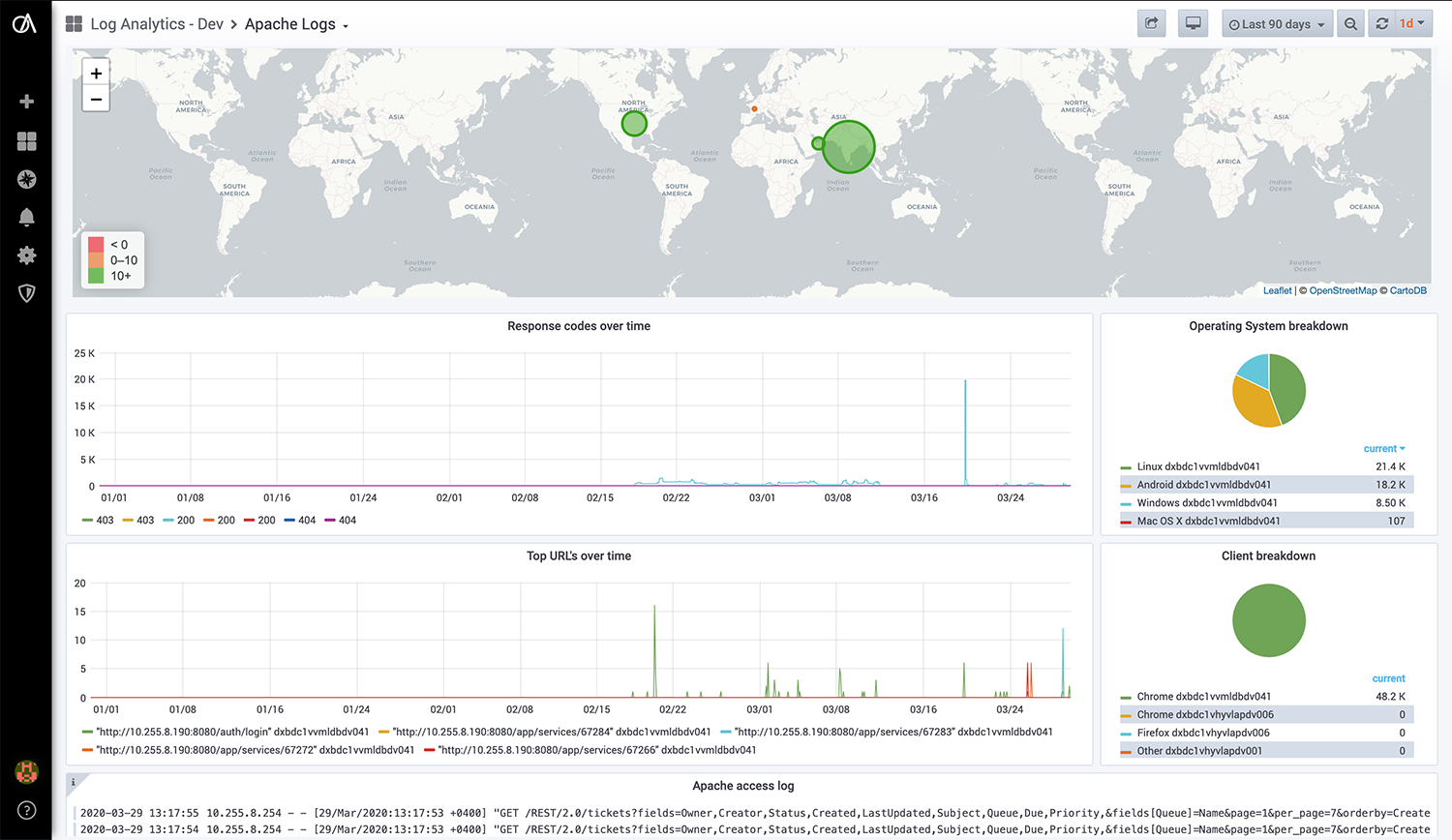
Enterprises growingly are vulnerable to data breaches. As the data collected and retained by the enterprises grow they become prime targets for malicious attacks leading to lost credibility and revenue. Increasing technology footprint also increases the effort to keep the systems up to date with patches, vulnerability assessments and vendor recommendations for fixes. LAAS provides the capability to monitor and scrub logs to identify malicious attacks. Real time notification upon an attack or identify a pattern of questionable code injection is invaluable to organizations. LAAS provides the capability to monitor and alert in real time by analyzing and scrubbing logs data of traffic on perimeter network devices, firewalls, Systems and application servers or 3rd party tools from a central location. Integrated with ITAMS, ITIMS and ITPAM demonstrates the value of data powered by DevOps.